Streamline Your Software Inventory
The expansion into cloud-native applications and infrastructure has created a phenomenal transformation for developers, where they can go from code to cloud in hours. But, legacy application security systems and processes impede security teams from knowing what risks are being introduced by the code being built and how to manage that risk.
Comprehensive Inventory
Within minutes gain visibility on all of your software assets (code repos, containers, microservices, etc.) – from applications to infrastructure.
Super simple setup, with all sources integrated via API.
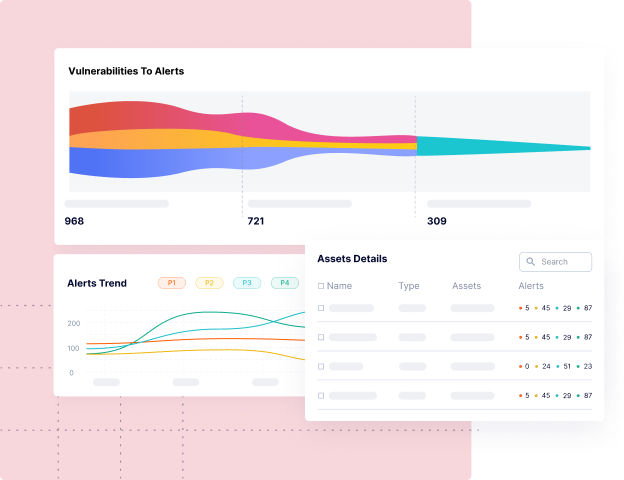
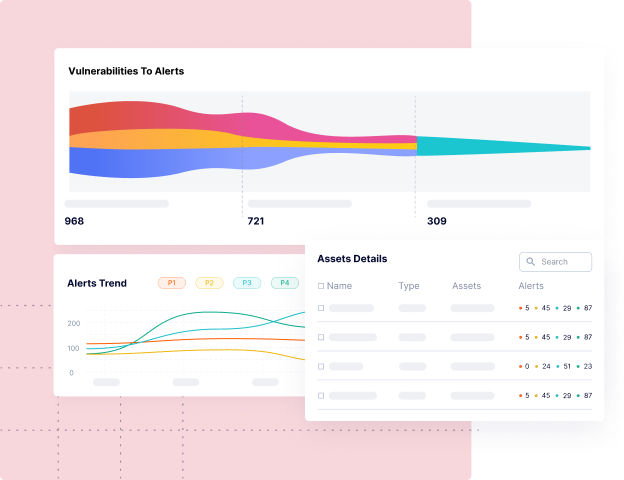
Understand Your Riskiest Assets
Know what assets are in production, Internet facing or business critical.
Prioritize assets with PHI/PII data or in scope of compliance.
Quickly triage assets posing the highest risk, across tools like SCA, SAST, DAST, CSPM, and more.
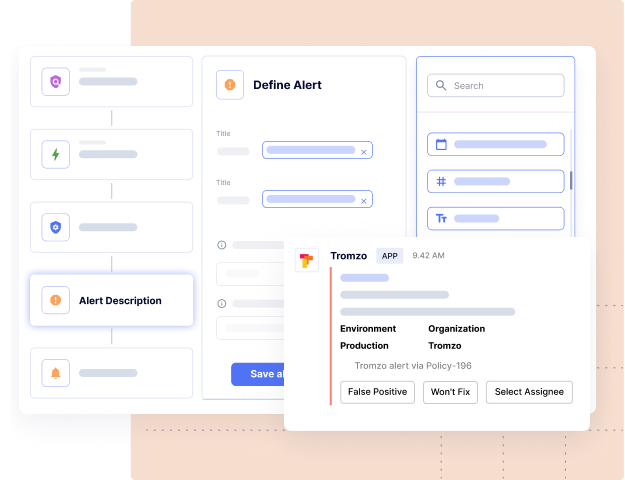
Clear Asset Ownership
Know exactly which team owns what assets across the full stack.
Automated discovery of ownership (Okta, GitHub teams, ADFS, AuthO, etc.) mapped to software assets.
Leave no gaps in ownership, accountability, or authority.
Ensured Compliance
Ensure 100% scan coverage for all software assets.
Drive policy compliance with security scoring for every asset.
Continuously measure KPIs like MTTR, SLA compliance, etc. across internal teams, services, and assets.
How Tromzo Can Help
Tromzo’s unified Product Security Operating Platform (PSOP) brings security visibility and control to the entire software lifecycle from code to cloud, so your organization can build secure software, fast!
Discover Artifact Inventory & Risk Posture
Contextual software asset inventory (code repos, software dependencies, SBOMs, containers, microservices, etc.), so you know what you have, who owns them, and which ones are important to the business.
Drive Real Vulnerability Remediation at Scale
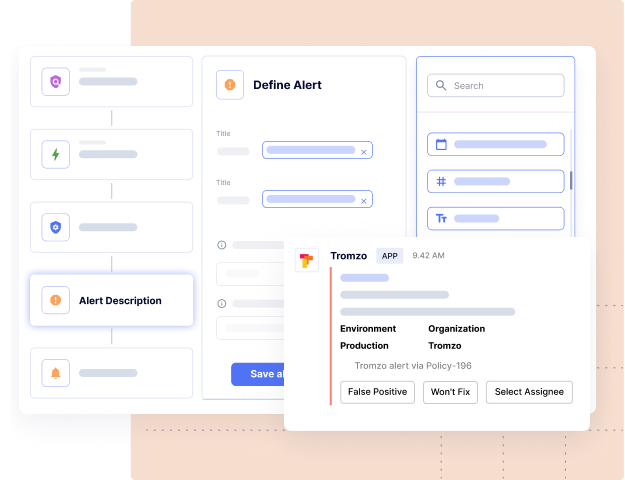
Leverage context from Intelligence Graph to tune out the noise and automate the remediation lifecycle, so you can eliminate the manual processes of triaging, prioritizing, associating ownership, risk acceptance, and compliance workflows.
Achieve a Data Driven Security Program
Understand the security posture for every team with SLA compliance, MTTR, and other custom KPIs, so you can drive risk remediation and accountability across the organization.
Risk-Based Application Security Management Platform
Contextualized Data. Security Guardrails. Automated Workflows.
Tromzo is a unified platform to incorporate security throughout the modern SDLC.
Recent articles in our Blog
On a recent episode of the Future of Application Security podcast, Chad Girouard, AVP Application Security at LPL Financial, talked about some of the challenges to overcome...
Read moreOn a recent episode of the Future of Application Security podcast, Dave Ferguson, Director of Technical Product Management, Software Supply Chain Security at ReversingLabs, explained why the...
Read moreReady to Scale Your Application Security Program?
Sign up for a personalized one-on-one walkthrough.